Image Credit: Canva
Note from The Tennessee Conservative: Editorial statements in this column are the sole opinion of the author; they do not necessarily reflect the opinions of the staff of this publication.
Submitted by Kathy Harms (Tennessee Fair Elections) –
Artificial intelligence is no longer just generating deepfakes and robocalls. It is now writing and testing computer code, helping attackers search for weaknesses in the software that runs everything from banks to hospitals AND elections.
National security and election security experts warn that AI doesn’t create brand new threats so much as supercharges the ones we already knew about, especially hidden flaws in voting machines, electronic pollbooks, and voter registration systems.
That should be a wakeup call for Tennessee, because we have quietly built an election model that depends on complex software working almost perfectly.
Early voting vote centers now handle most of the ballots in many counties. Those sites rely on statewide voter registration databases, networked electronic pollbooks, ballot on demand printers, and ballot marking devices all working together. A subtle coding error or new vulnerability in any one of those components can ripple through a huge share of the county’s vote before anyone notices.
In an AI era, we are making it easier for sophisticated attackers to find and exploit those weak spots at machine speed. We already have proof that traditional testing and certification are not enough.
In Georgia, a federal court unsealed a 96 page expert report by University of Michigan professor J. Alex Halderman analyzing the Dominion ImageCast X ballot marking devices used statewide.
Halderman showed how attackers with physical access could install malware to change votes, alter QR codes, or spread to other machines, all without easy detection. The Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency urged that these flaws be “mitigated as soon as possible.”
Yet Georgia announced it would wait until after the 2024 presidential election to install Dominion’s software update, leaving known vulnerabilities in place for a high stakes contest. As Halderman warned, announcing that delay “makes the problem far more dangerous” because it tells attackers exactly what unpatched system will be used and gives them time to prepare.
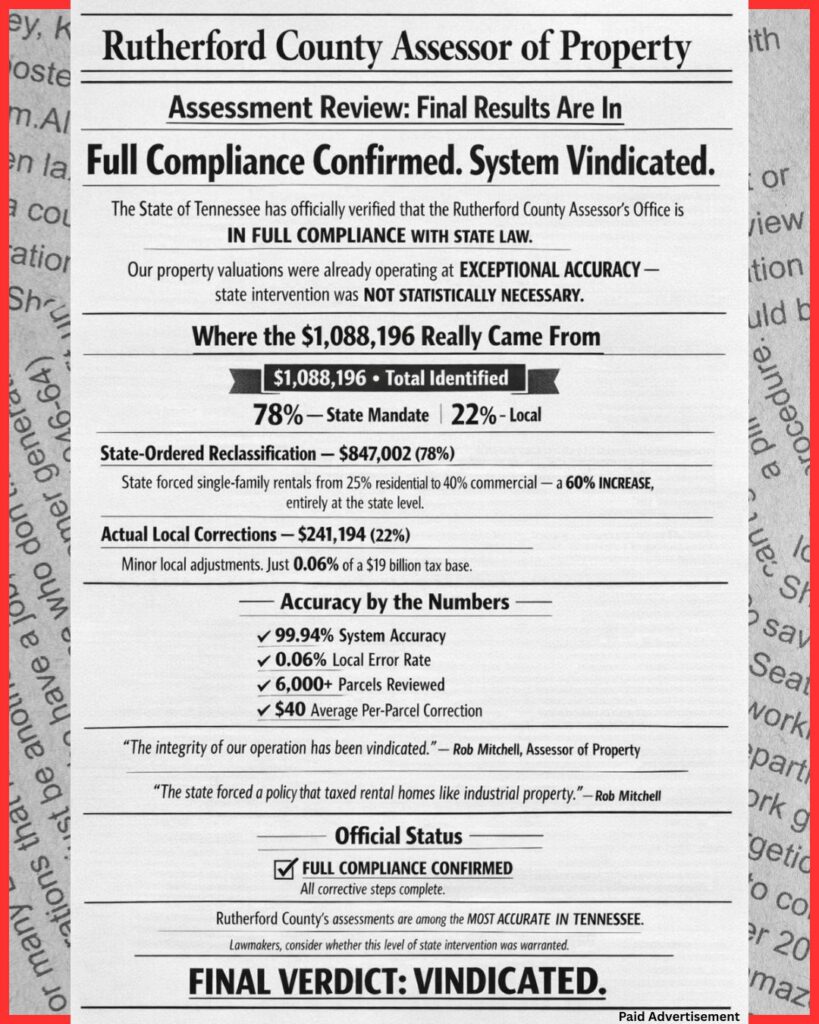
Closer to home, Williamson County experienced what the U.S. Election Assistance Commission (EAC) calls a “voting system anomaly” during a Franklin city election in October 2021.
Some ballots that were successfully scanned and tabulated by Dominion scanners did not appear on the closing results tape, forcing a hand count and rattling public confidence.
After investigation, the EAC concluded that an “isolated coding issue” in the certified system caused certain ballots to be miscategorized. The official diagnosis? “The direct cause of the anomaly was inconclusive.” In plain English: a small software error in a federally tested, state approved voting system was enough to misclassify real ballots in a Tennessee election.
Independent experts have shown how fragile these systems can be. At the DEF CON Voting Machine Hacking Village, researchers and students were allowed to test dozens of voting machines and electronic pollbooks.
By the end of the conference, “every piece of equipment in the Voting Village was effectively breached in some manner,” often by people with no prior experience on those devices. The Center for Internet Security (CIS), which supports state and local election oƯices, warns that vulnerabilities in third-party software, firmware, and development tools create serious risks across the election technology supply chain—and that onetime certification cannot keep up with how fast new weaknesses are discovered.
AI makes all of this worse. The Brennan Center for Justice has warned that AI tools can help attackers develop or improve malware and increase the volume and sophistication of attacks on election infrastructure. Cyber analysts report that AI is being used to automate software supply chain attacks, including tampering with development tools and build pipelines—the exact path that could plant hidden flaws into election software before it ever reaches a county office. AI gives an adversary the equivalent of thousands of DEF CON hackers working in parallel around the clock.
Taken together, what Halderman found in Georgia, what the EAC documented in Williamson County, what DEF CON and CIS have shown about the broader ecosystem, and what AI is now doing to accelerate code level attacks all point in the same direction: highly centralized, heavily computerized voting architectures are fragile by design.
Tennessee does not have to keep gambling that our vote center model will avoid the next bug or exploit. There is a better option already allowed under Tennessee law: precinct based voting with hand-marked paper ballots. State statute expressly contemplates voting by paper ballot at the polling place. Counties are not prohibited from using hand-marked paper ballots in neighborhood precincts; they have simply grown accustomed to vote centers and been reassured that convenience is worth the risk.
Hand-marked paper ballots at local precincts directly address the vulnerabilities exposed by all this research:
• Voters mark their own ballots by hand, eliminating entire categories of ballot marking device and QR code manipulation.
• A problem in one precinct, whether a bad scanner, a power outage, or a procedural error, aƯects that precinct, not the entire county.
• If a precinct scanner fails or there is a question about results, ballots can be recounted by hand in that precinct with observers present. Williamson County learned this the hard way when its software failed and oƯicials had to fall back to a hand count.
• Precinct based voting can operate from printed pollbooks or offline local lists, greatly reducing the opportunity for real-time manipulation of who can vote and where.
We don’t have to abandon technology. Optical scanners can still count hand-marked ballots quickly and support audits. Electronic systems can still manage statewide registration and produce precinct pollbooks. But in an AI era, the most critical steps, who gets a ballot, how it is marked, and how many ballots are in each neighborhood, should rest on simple, observable processes, not on opaque software that AI assisted attackers are now systematically probing for weaknesses.
The message is not that our election officials are corrupt. The message is that our current, highly centralized, heavily computerized vote center model makes it too easy for hidden problems to have large effects. Tennessee counties already have the legal authority to use precinct based hand-marked paper ballots. In the age of AI driven attacks, they should start exercising it.